Cisco Midyear Security Report
This report covering a number of cybersecurity threats currently assailing corporate networks obviously focuses on Cisco’s response but may be of interest to subscribers. Here is the conclusion:
The threats discussed in this report represent only a small sample of the cybersecurity challenges that organizations, their security teams, and individual users face. So far, 2015 is proving to be a year of unprecedented speed in the innovation, resiliency, and evasiveness of cyberattacks. Adversaries are intent on overcoming all barriers to their success. As fast as the security industry can develop technologies to block and detect threats, miscreants pivot or change their tactics altogether.
?The innovation race between adversaries and security vendors is only accelerating, and organizations are at risk of becoming more vulnerable to attack if they sit back and watch. They need to be proactive about identifying and addressing cybersecurity risks that can affect their business and aligning the right people, processes, and technology to help them meet those challenges.
“Security needs to be part of the way organizations think—holistically—about their business,” says David Goeckeler, senior vice president and general manager for the Security business group at Cisco. “There is a great deal at stake: their brand, their reputation, their intellectual property, and their customers’ data. All of these things are at risk. Organizations need to take a systemic approach to minimizing that risk through an appropriate security posture.”
Trustworthy products are an essential component of an effective security posture, says John N. Stewart, chief security and trust officer for Cisco. “Organizations no longer want to accept that compromise is inevitable,” he says. “They are looking to the security industry to provide them with products that are reliable and resilient, and capable of deflecting even the most sophisticated threats.
Here is a link to the full report.
Cybersecurity is a cause celebre for those of us who have had our credit card details stolen or had to endure letters from corporations telling us our most personal data “may” have been included in that which was stolen during a multi-month breach they previously knew nothing about. The investment crowd has priced in a substantial amount of good news already and valuations have increased particularly for those spearheading the sector’s advance.
Let’s spilt the sector between those companies providing infrastructure software such as Palo Alto from those providing infrastructure hardware such as Cisco. The vast majority of new companies provide software solutions but there is an argument if a network is to be secured, the approach should start with hardware.
While software companies have been receiving a great deal of media attention the infrastructure sector has been much slower to gain attention not least because of the significant capital required in making decisions on whether to build new networks. There are a relatively small number of companies that dominate this sector because the barrier to entry is so high.
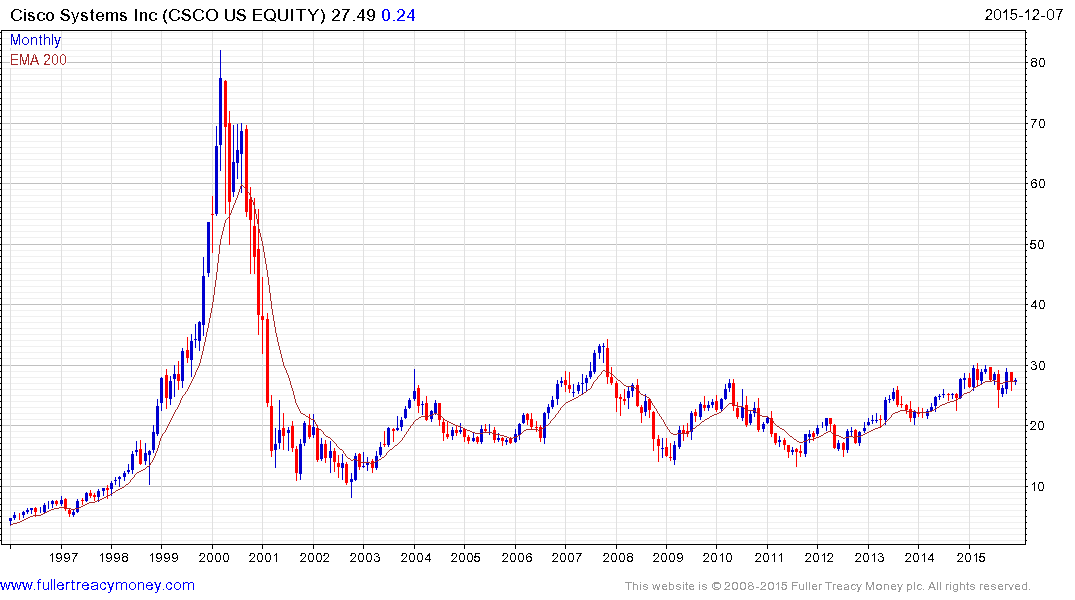
Cisco Systems (Est P/E 12.12, DY 3.07%) has been ranging below its 2007 peak and the upper side of the 15-year range for the last year. It has held a medium-term upward bias since 2011 but will need to sustain a move above $30 to signal a return to demand dominance.
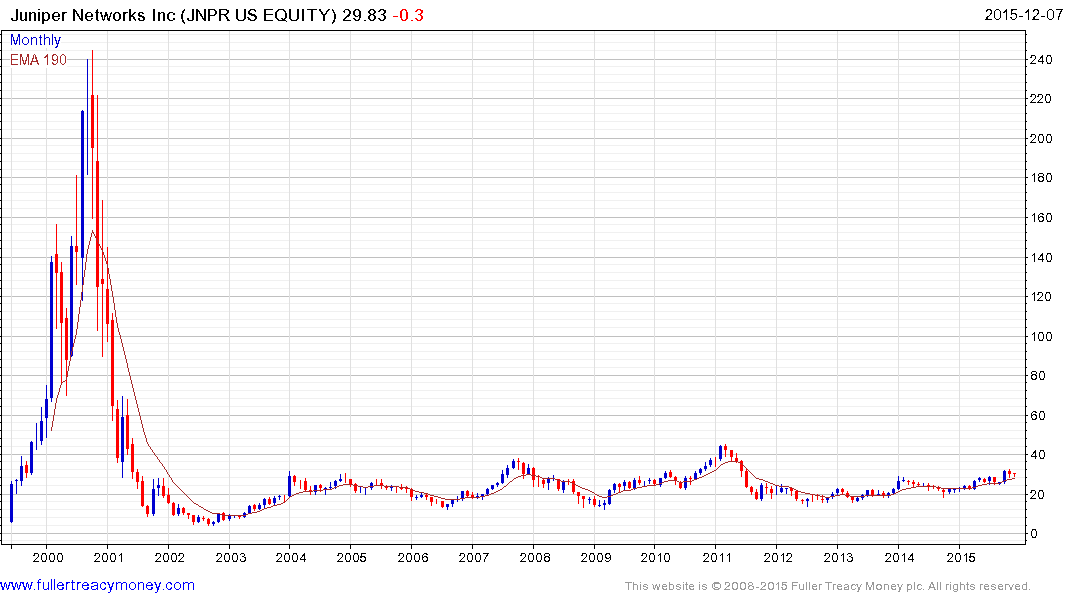
Juniper Networks (Est P/E 14.93, DY 1.34%) has been confined to a lengthy base formation since 2001 but has held a progression of higher major reaction lows within it since 2012. A sustained move below $25 would be required to question the medium-term upside bias.

F5 Networks (Est P/E 14.68, DY N/A) has been largely rangebound since accelerating to its 2010 peak. It found at least near-term support in the region of $100 last week and a sustained move below that level would be required to question potential for a reversionary rally.
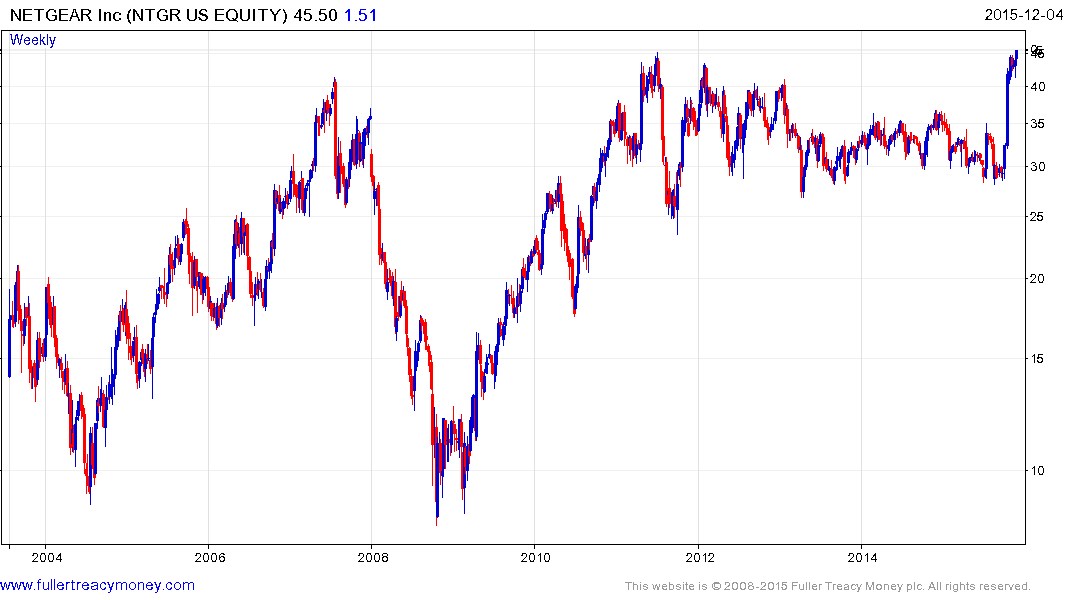
Netgear (Est P/E 21.92, DY N/A) has surged over the last month to test the 2011 peak and some consolidation of that gain is likely which would allow the short-term overbought condition to be unwound. A sustained move below the $35 area would be required to question medium-term scope for additional upside.
Back to top


